Password managers have been talked about for a while now, but how are they different from just memorising your secret phrases to access online realms? Well, long are gone the days when you had just an email account and one social media profile. Perhaps, if you had niche interests, you visited a dedicated forum which required an additional password. Now, we have an app for everything, meaning that you have more passwords to memorise.
And with the cyber attackers constantly evolving, a simple “FavouritePetName2001” does not suffice anymore as the key to your personal online presence.
In this article, I am going to delve into the depths of accounts and passwords from a security engineer’s point of view, suggesting ideas you may have not yet given a thought. And I hope you will see the benefit and importance of password managers when it comes to your online privacy.
The origin of passwords
In older times, at nightfall, any guards or townspeople traveling outside of the gates were considered suspects. It's hard to identify who, or how many there are on the other side of the door without exposing both parties to danger.
So, a password was set with people venturing outside. It could be as simple as a question about one's family and friends, or information about recent ongoings. Mostly a simple dedicated question with a pre-approved answer. Maybe this is also familiar from spy movies or other war stories.
These days we use passwords daily. No service provider trusts users without explicit authentication. If you were to call your phone company or bank, they would first like to know who they are talking to. Similarly, with all of the online services, your account is not only for advertisement purposes.
The illusion of password secrecy
Passwords are an integral part of our digitalised society. But they are not always as secret as you think they are. Password is something you get to choose as a user – you openly disclose this shared secret with the other party.
Most service providers that use modern best practices will not know your password directly, but an amalgamation of a secret they chose and the one you chose – one common example being the "salted hash".
But what about that web forum you registered for decades ago? Or the web shop that's asking you to register an account? Are they using the best practices or do they save the password directly in their database? It used to be a commonplace practice, and even now some service providers get called out from time to time.
If you have ever clicked the "I have forgotten my password" link and gotten your password in your mailbox plaintext without any extra protection, then they can clearly read your password. And now your email provider can as well, this mail resides on their server, after all.
For example, check out these exposure offences collected for the past 10 years.
And herein lies the weakness of password reuse – even if one site gets compromised, your every other account with the same password is at risk of takeover. This is especially painful in the times of password breaches, where your chosen password is often made public.
The solution to password reuse
It is understandable that, considering the average human’s memory, you simply cannot remember too many unique passwords containing uppercase letters, special symbols etc. This is when passwords managers come in handy – you can safely store your strong passwords in there. These days users may have hundreds of online accounts – from multiple social media accounts to online shopping sites, emails, niche portals and even e-health providers.
To simplify the log in process, many services providers offer you to sign in with a social media or another account, bypassing the native account creation which means one less password to remember. Trusting the service provider to act in good faith and maybe bypassing the need for a password manager.
But do you really want Facebook, Google, Apple, Microsoft or the likes to have a direct access to all of your other accounts? Federated identities may help in case you do. As in that "Log in with your favourite service" button, where you forego passwords in favour of reusing your existing account.
Additionally, does your employer really need to know the password to your personal email? Because that's what you are sharing when reusing passwords. On that note, check if your email address has been in a data breach.
So, a unique new secret for each and every account is needed. There are schemes for generating seemingly strong passwords – check out this comic for one example:
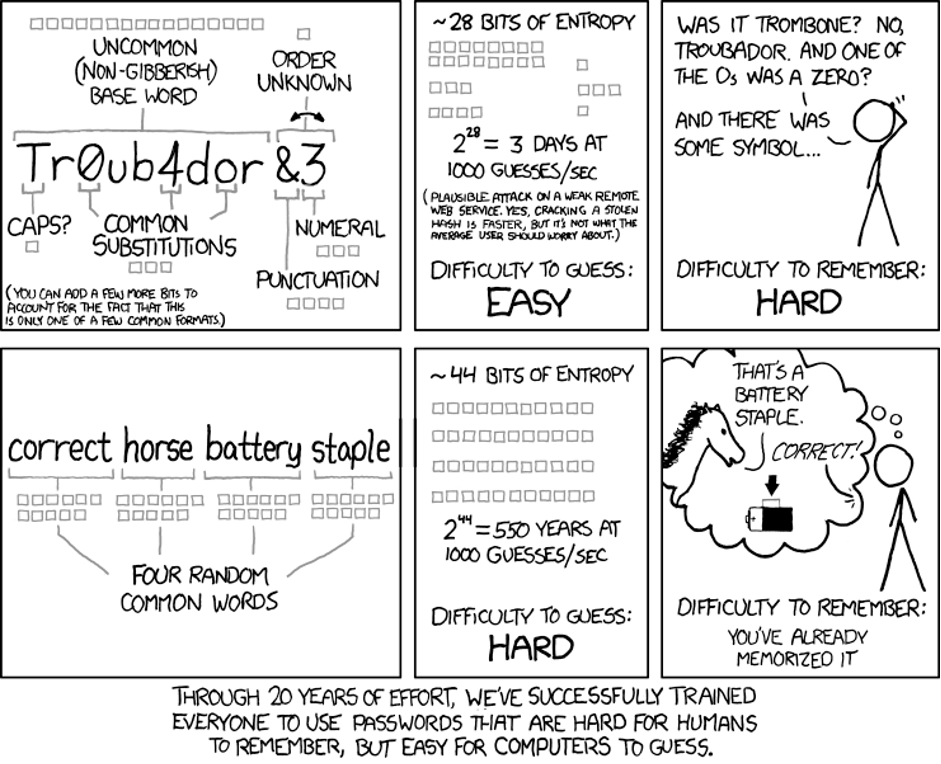
Copyright of XKCD.com under the Creative Commons Attribution-NonCommercial 2.5 License.
But all of these schemes have their weaknesses – check out a compilation of sites with dumb password rules.
These days, people have evolved to use software for this task. And it's even free! Online password managers may offer limited functionality unless you pay, but others are open source and made entirely from the goodwill of the developers – they need their own passwords managed as well.
How to choose a password manager?
The general consensus is that using a password manager is better than not using one – even if it only means that users stop reusing their passwords.
For the most basic option, vendors offer their services with a password manager like Apple iCloud Keychain or Google Password Manager. As do all major web browser vendors like Google Chrome, Mozilla Firefox and Microsoft Edge.
For most users this is a good option to get started, but for the paranoid, there are further considerations. To answer straight away, the most secure password manager that does not sacrifice features is KeePassXC.
KeePassXC is a well-regarded, open-source password manager with secure offline storage. It's compatible with multiple devices and can be used on all major operating systems.
And if you need to use your password on multiple devices, just keep the database file in sync via your favourite cloud drive (Dropbox, Google Drive, OneDrive etc) or a custom solution (Syncthing, memory stick, even carrier pigeons).
But to help you make a better decision, here are 5 things to consider when choosing a password manager:
- Security and privacy: look for managers that offer two-factor authentication (2FA) options and are known for strong security measures. Check if they have open-source encryption or zero-knowledge protocols, ensuring your data is protected from potential breaches.
- Platform compatibility: verify whether the chosen password manager offers apps for multiple devices and platforms to provide a seamless user experience across all devices.
- Pricing plans: assess if the password manager offers both free and premium plans with varying features, allowing users to select an option that suits their needs best. Premium plans may include additional security tools, customer support, and cloud storage.
- Ease of use: Evaluate each password manager based on its interface and usability for different user groups (e.g., beginners, tech-savvy users). Check if the app has a user-friendly interface and offers helpful features such as auto-fill capabilities and browser extensions.
- Additional features: some password managers may offer extra security features, such as dark web monitoring or secure file storage. Consider which additional tools would be beneficial to you or your organisation.
Should you opt for a cloud-based manager, below are the most notable providers:
- LastPass: offers security with two-factor authentication, and a user-friendly interface. It's available on multiple devices, and offers free and premium plans. Has had multiple security breaches, but seems to still be trusted by some users. Hope the users affected had really strong master passwords, and started rotating all of their passwords right after the breach was made public. More info here.
- 1Password - known for its secure storage and password generation features. It supports many platforms, including mobile and desktop apps, and has a wide range of pricing options.
- Dashlane - offers top-notch security with zero-knowledge encryption and built-in VPN support. The plan includes a dark web monitor and password health tools to ensure your online safety.
- Bitwarden: provides an open-source platform with strong encryption for peace of mind and offers various plans, including a free option for personal use. It has apps or browser extensions for all major platforms, making it easy to access your passwords wherever you need them.
And if you are worried about being targeted, there are simpler ways to break security:
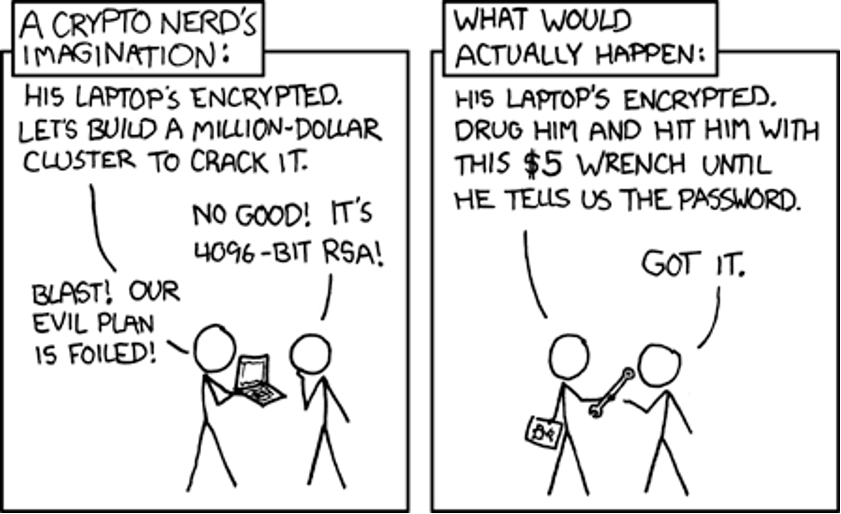
Copyright of XKCD.com under the Creative Commons Attribution-NonCommercial 2.5 License.
Some secrets are worth more than others – choose your vault wisely
When using a password manager, specific care should be taken when handling secrets with more power than normal. Even using best practices, a compromise may be so costly that it may be cheaper to select an alternative storage approach.
For example, your work SSO login password – this password has the ability to log into nearly all of your work-related services, sometimes without any limits. This is probably already against the security policy of the company, and could make you personally liable to a costly security breach.
It could be especially dangerous if passwords and second factor tokens are stored together. If your password manager was to get compromised, storing both factors together ready for the attacker to use might not be the best idea. The recommendation is to backup these in a separate way. Either use another password manager vault, write them on a piece of paper in your home safe, or the best option yet: register two devices right away – one for daily use and the other for backup – such as an old phone.
The future
Password managers are a great technology, and they are here to stay for many users. But innovation keeps happening, and if you need to secure just your major accounts, as well as want to get rid of passwords altogether, then passkeys could be your solution.
WebAuthn is a web standard replacing login flows all across the internet. This is a technology that replaces the “something you know” part of the authentication flow with “something you have”, in addition to “something you do” – like plugging the key in, or pressing a button.
These devices could be a chip in your smartphone, a Bluetooth wireless token or a USB key. For example, Yubikey Bio is a WebAuthn compatible device, where in order to use it, you need to also provide “something you are” in the form of a fingerprint.
Passkeys could replace passwords in their entirety, and make password managers an obsolete technology even before total adoption. Until then, please make an effort to stop password reuse and suggest using a password manager for the people around you.
